Active Directory security
AIOps (artificial intelligence for IT operations
API Management for IT Tools
Application attacks (buffer overflows, cross-site scripting)
Application attacks (buffer overflows, cross-site scripting)
Application integration architecture
Application Lifecycle Management (ALM)
Application Maintenance on Production Systems
Application Rollout Planning and Problems
Application security and coding requirements
Application Virtualization
Artificial Intelligence (AI)
Artificial intelligence and analytics
Artificial intelligence, automation and robotics
Azure, Google and other public cloud providers
Backing up VMware host servers and guest OSes
Backup and recovery software
Best practices for data center operations
Bring Your Own Device (BYOD) security
Building Software Project Teams
Business automation and robotics
Business Intelligence (BI) management
Business intelligence strategy
Business Process Management (BPM)
Business Video Conferencing and Telepresence Technology
BYOD and mobile device security best practices
Capacity planning for virtualization
Channel Partner Programmes
Chief Information Officer (CIO)
Chief Technology Officers (CTO)s
CIO career development and career paths
Cloud APIs and frameworks
Cloud application development and deployment
Cloud architecture design
Cloud architecture design and planning
Cloud computing architecture
Cloud computing pricing and economics
Cloud development and testing
Cloud management and monitoring
Cloud Network Security Trends and Tactics
Cloud Provisioning and Cloud Identity Management Issues
Cloud storage management and standards
Cloud-SaaS content management (ECM)
Collaboration Applications for Unified Communication
Collaborative Applications
Commerce and e-commerce strategy
Commerce technology and strategy
Communication Integration with Enterprise Applications
Computer storage hardware
Configuration Management and DevOps
Content delivery networks (CDNs)
CRM technology and software decisions
Customer experience management
Customer experience management strategy
Data center budget and culture
Data center design and facilities
Data Center jobs and staffing and professional development
Data center server infrastructure and OSes
Data center systems management
Data Destruction Techniques
Data integration technology
Data management-as-a-service (DMaaS)
Data protection regulations and compliance
Data quality management software
Data reduction and deduplication
Data security in the cloud
Data security strategies and governance
Data security strategies and governance
Datacenter Infrastructure News and Expert Advice
Datacentre capacity planning
Datacentre performance troubleshooting, monitoring and optimisation
Datacentre systems management
DDoS attack detection and prevention
Developers' Tools and Resources
DevOps and IT Certifications and Training
Digital business transformation
Digital business transformation and innovation
Disaster recovery planning - management
Disaster recovery services - outsourcing
Disk and file encryption tools
Distributed application architecture
dual persona (mobile device management)
EAI (enterprise application integration)
Electronic medical records security and data loss prevention
Email and messaging threats
Emerging cyberattacks and threats
Emerging IT workload types
EMM tools | Enterprise mobility management technology
Employee engagement and recognition software
Employee recruitment software
Endpoint protection and client security
Enterprise applications of AI
Enterprise artificial intelligence (AI
Enterprise content management (ECM) technology
Enterprise content management (ECM) workflow
Enterprise content management, collaboration and search strategy
Enterprise data storage strategies
Enterprise desktop management
Enterprise document management software
Enterprise infrastructure management
Enterprise Java development
Enterprise mobile security
Enterprise mobility strategy and policy
Enterprise SharePoint strategy
Enterprise tips, tricks and best practice implementation
Enterprise Web content management software
Event-driven architecture, CEP and operational intelligence
Exchange Server Management
Exchange Server setup and troubleshooting
Exchange Server setup and troubleshooting
Expert Enterprise Technical Advice (EETA)
Hackers and cybercrime prevention
How-Tos and Other Simple Explanations
HR and artificial intelligence
HR systems and HCM software
Hybrid and Private Cloud Computing Security
Hybrid Cloud Architecture
Hyper-Converged Infrastructure Implementation
Hyper-Converged Infrastructure Management
Hyper-Converged Vendors and Products
Identity and access management
Implemented Solution Use Cases
Improving server management with virtualization
Industrial automation software
Information management strategy
Information security incident response
Information security incident response
Information security laws, investigations and ethics
Information security threats
Infrastructure (IaaS) cloud deployment strategies
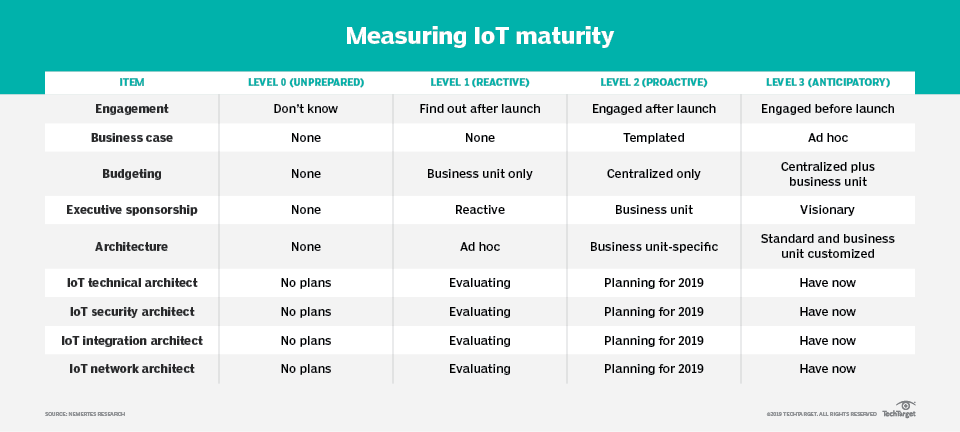
Internet of Things (IoT) and ERP
Internet of Things (IoT) Data Management
Internet of Things (IoT) Hardware
Internet of Things (IoT) in Healthcare
Internet of Things (IoT) Security Strategy
Internet of Things (IoT) Standards and Certifications
Internet of Things (IoT) Strategy ALL
Internet of Things (IoT) Wireless
Intersection between politics and the information society.
IPv6 security and network protocols security
IT applications, infrastructure and operations
IT compliance and governance strategies
IT education and training
IT for retail and logistics
IT for retail and logistics
IT infrastructure management and planning
IT operations management and IT support
IT Research / Study Results
IT spending and budgeting
Kemaza technical resources for IT pros
Latest Flaws uncovered by Researchers
Latest security threats and mitigation
Leadership and strategic planning
Legacy Application Modernization for the Cloud
Machine learning modeling
machine vision (computer vision)
Malware, virus, Trojan and spyware protection and removal
Management Tools and Strategies
Managing Cloud-Native Applications
Managing Virtual Containers
Manufacturing production planning
Messaging and collaboration
Microservices and data integration
Microservices and development
Microservices pattern, platforms and frameworks
Microsoft Azure cloud services
Microsoft Hyper-V management
Microsoft identity and access management
Microsoft Office and Office 365
Microsoft Patch Tuesday and patch management
Microsoft Windows security
Microsoft Windows Server 2012
Microsoft Windows Server 2019
Mobile and wireless network technology
Mobile application security best practices
Mobile application security best practices
Mobile security threats and prevention
Mobile security threats and prevention
Multi-cloud managed services
Multichannel Customer Service
Multifactor authentication
Network application performance
Network Attached Storage (NAS) Solutions and Services
Network automation and intent-based networking
Network device security: Appliances, firewalls and switches
Network functions virtualization (NFV)
Network Infrastructure Solutions and Services
Network management and monitoring
Network management software and network analytics
Network protocols and standards
Network Security Best Practices and Products
Network Security Monitoring and Analysis
Network security strategy
Open source cloud computing
Open source security tools and software
Operating Systems and Software Services
Password management and policy
Pattern recognition and machine learning
Penetration testing, ethical hacking and vulnerability assessments
People analytics software ALL
Performance management software
Platform-as-a-Service (PaaS)
Podium: CIOs' and Thought Leaders' Interviews
Privacy and data protection
Privacy and data protection
Productivity apps and messaging security
Project Managers' Resources
Public cloud and other cloud deployment models
Public Cloud Computing Security
Real-time business intelligence
Real-Time Performance Monitoring and Management
Risk and compliance strategies and best practices
Risk management and compliance
SaaS business intelligence
Sales strategy and sales force effectiveness
SAN technology and arrays
SAP business intelligence
SD-WAN (software-defined WAN)
Secure software development
Securing a VMware environment
Selecting storage and hardware for VMware environments
Server hardware and virtualization
Server virtualization compliance and governance
SIEM and security analytics
Small-business infrastructure and operations
Small-business IT strategy
SOAR (Security Orchestration, Automation and Response)
Social HR and collaboration strategies
Software Configuration and Change Management
Software Development Fundamentals
Software Performance Management
Software Requirements Management
Software Test Design and Planning
Software Testing and QA Fundamentals
Software Testing and QA Fundamentals
Software Testing Tools and Frameworks
software-defined data center (SDDC)
software-defined networking (SDN)
Solution example and tips
SQL Server Database Compliance
SQL Server Management issues
SQL Server Migration Strategies and Planning
Stress, Load and Software Performance Testing
Supply chain planning and execution
supply chain sustainability (SCS)
Tape backup and tape libraries
Technical Caveats & Conundrums
Technical Questions Answered by Experts
Tekmart hardware maintenance tips
Tekmart South Africa's Datacenter Products
Telecommunication networking
Test-Driven and Model-Driven Development
Text analytics and natural language processing software
troubleshooting and alerting
Two-factor and multifactor authentication strategies
Unified Communication (UC)
Unified Communications Architecture and Service Models
Unified Communications Integration and Interoperability
Unified Communications Security
Useful definitions to know...
Vendor Software Vulnerability Security Patch Latest News
Virtual desktop infrastructure and architecture
Virtual desktop management
Virtual desktop strategies and architecture
Virtual desktop tools and technology
Virtual machine monitoring
Virtual machine performance management
Virtual machine provisioning and configuration
Virtualization How-Tos and guides
Virtualization vendor comparisons
Visible light communication (VLC)
VMware cloud computing tools
VMware ESX and ESXi administration
VMware ESX and ESXi administrative
VMware host servers and guest OSes
Voice and unified communications
VoIP Migration and Implementation
Web application and API security best practices
Web authentication and access control
Web server threats and application attacks
Windows 10 security and management
Windows administration tools
Windows systems and networks
Wireless and mobile security
Your Opinion-What do you think?